Frontiers | Individual-based and interactional resilience mechanisms in social and healthcare service NPOs during the COVID-19 pandemic: Handling a disruptive extreme context in Austria
PDF) Ethical approval: none sought. How discourse analysts report ethical issues around publicly available online data
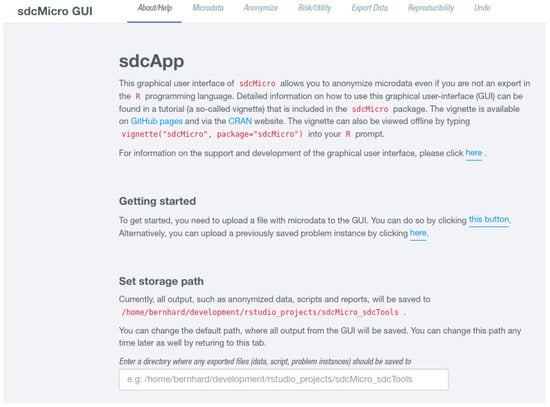
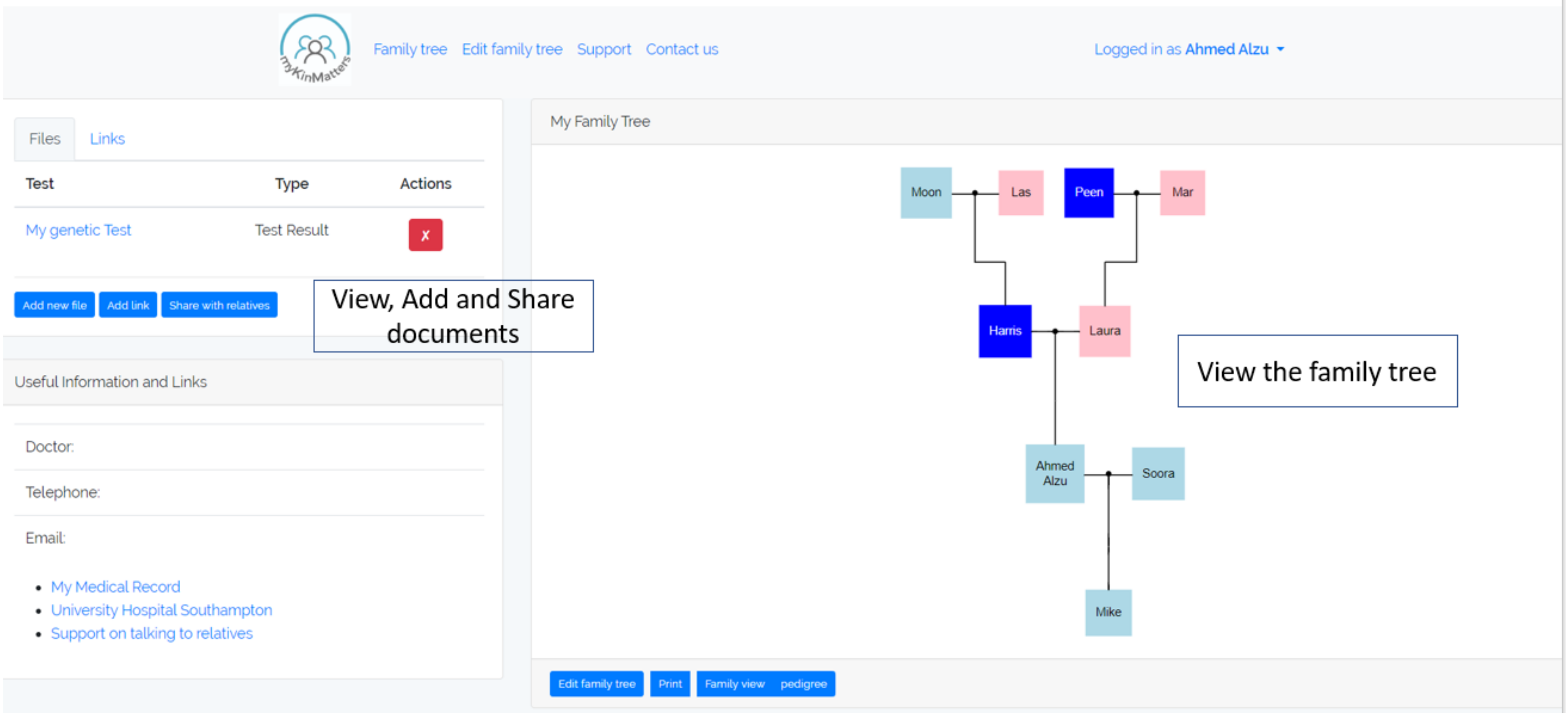
Algorithms | Free Full-Text | Feedback-Based Integration of the Whole Process of Data Anonymization in a Graphical Interface

PDF) Quasi-Identifier Recognition Algorithm for Privacy Preservation of Cloud Data Based on Risk Reidentification
Ethical review of COVID-19 research in the Netherlands; a mixed-method evaluation among medical research ethics committees and i
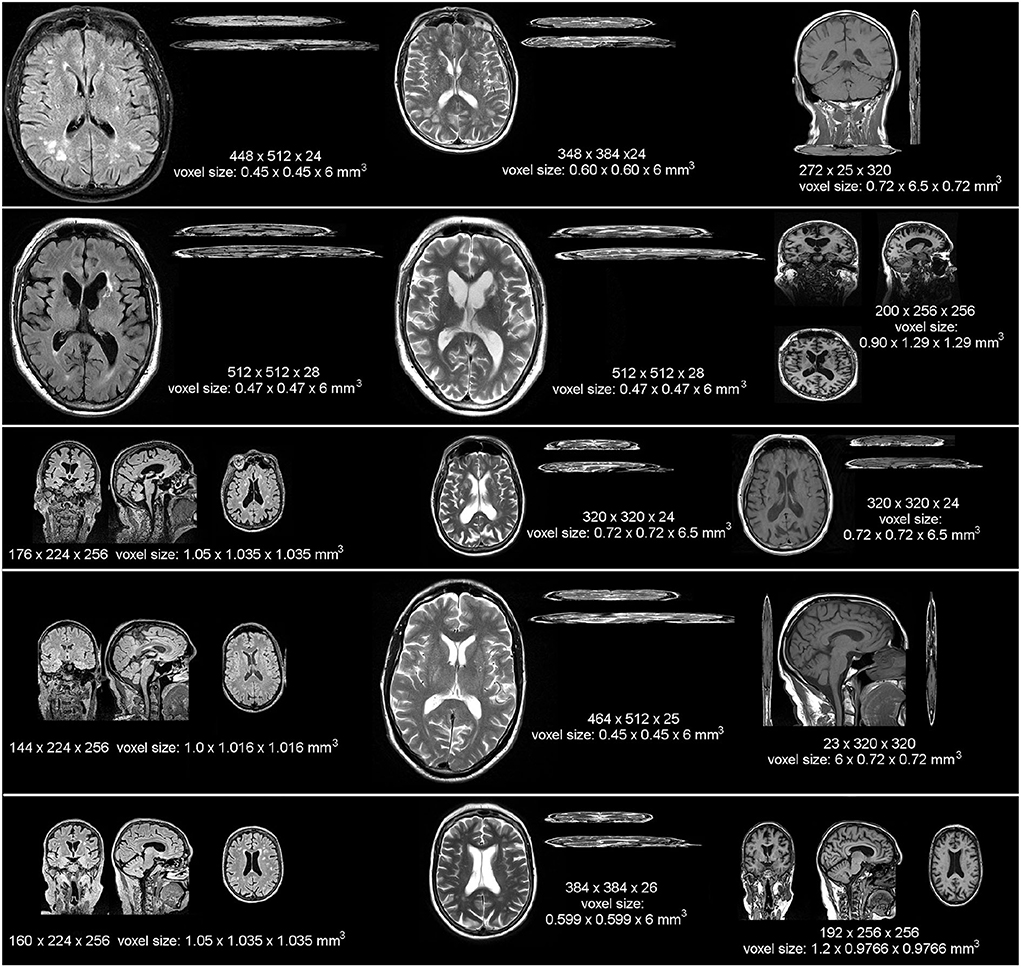
Frontiers | Deep attention super-resolution of brain magnetic resonance images acquired under clinical protocols

A γ‐Strawman privacy‐preserving scheme in weighted social networks - Chen - 2016 - Security and Communication Networks - Wiley Online Library

A γ‐Strawman privacy‐preserving scheme in weighted social networks - Chen - 2016 - Security and Communication Networks - Wiley Online Library

How Do Tor Users Interact With Onion Services PDF | PDF | Tor (Anonymity Network) | Domain Name System
Virtual punishment in the making: When citizen journalism enables processes of shaming and online victimization Mallén, Agneta

Privacy issues in social networks and analysis: a comprehensive survey - Pham - 2018 - IET Networks - Wiley Online Library

%20(002)NEOGOVWEBSITE.png)